About the secret scanning alerts page
When you enable secret scanning for a repository or push commits to a repository with secret scanning enabled, GitHub scans the contents for secrets that match patterns defined by service providers and any custom patterns defined in your enterprise, organization, or repository.
When secret scanning detects a secret, GitHub generates an alert. GitHub displays an alert in the Security tab of the repository.
To help you triage alerts more effectively, GitHub separates alerts into two lists:
- High confidence alerts.
- Other alerts.
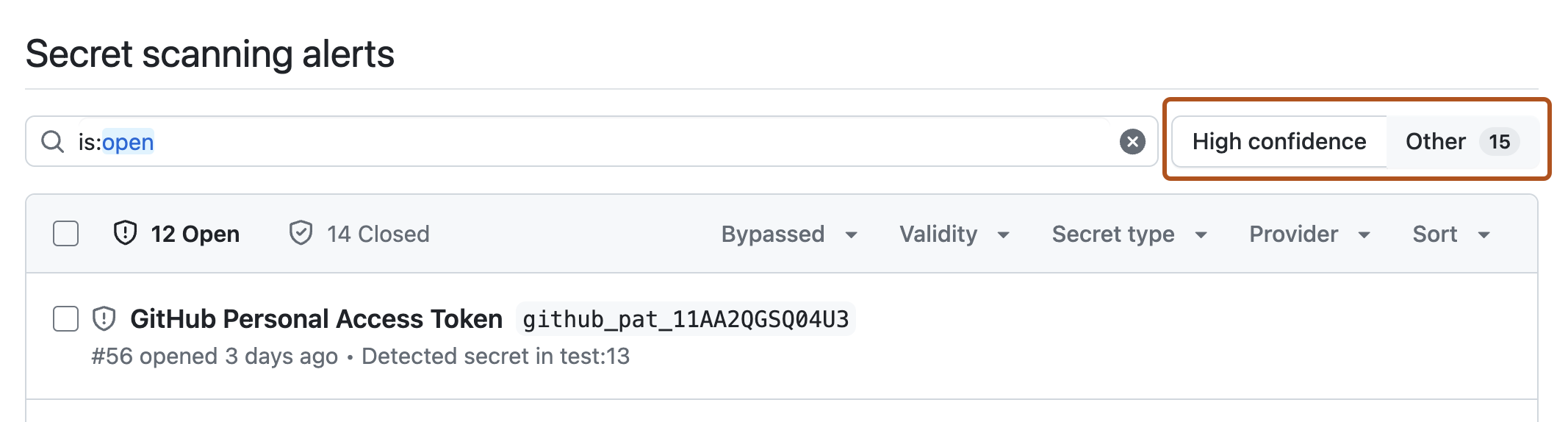
High confidence alerts list
The "High confidence" alerts list displays alerts that relate to supported patterns and specified custom patterns. This list is always the default view for the alerts page.
Other alerts list
The "Other" alerts list displays alerts that relate to non-provider patterns (such as private keys). These types of alerts have a higher rate of false positives.
In addition, alerts that fall into this category:
- Are limited in quantity to 5000 alerts per repository (this includes open and closed alerts).
- Are not shown in the summary views for security overview, only in the "Secret scanning" view.
- Only have the first five detected locations shown on GitHub for non-provider patterns.
For GitHub to scan for non-provider patterns, you must first enable the feature for your repository or organization. For more information, see Enabling secret scanning for non-provider patterns.
Viewing alerts
Alerts for secret scanning are displayed under the Security tab of the repository.
-
On GitHub, navigate to the main page of the repository.
-
Under the repository name, click Security. If you cannot see the "Security" tab, select the dropdown menu, and then click Security.

-
In the left sidebar, under "Vulnerability alerts", click Secret scanning.
-
Optionally, toggle to "Other" to see alerts for non-provider patterns.
-
Under "Secret scanning", click the alert you want to view.
Note
Only people with admin permissions to the repository containing a leaked secret can view security alert details and token metadata for an alert. Enterprise owners can request temporary access to the repository for this purpose.
Filtering alerts
You can apply various filters to the alerts list to help you find the alerts you're interested in. You can use the dropdown menus above the alerts list, or input the qualifiers listed in the table into the search bar.
| Qualifier | Description |
|---|---|
bypassed | Display alerts for secrets where push protection has been bypassed (true). For more information, see About push protection. |
confidence | Display alerts for high-confidence secrets which relate to supported secrets and custom patterns (high), or non-provider patterns such as private keys (other). See Supported secret scanning patterns. |
is | Display alerts that are open (open) or closed (closed). |
props | Display alerts for repositories with a specific custom property (CUSTOM_PROPERTY_NAME) set. For example, props:data_sensitivity:high display results for repositories with the data_sensitivity property set to the value high. |
provider | Display alerts for a specific provider (PROVIDER-NAME), for example, provider:github. For a list of supported partners, see Supported secret scanning patterns. |
repo | Display alerts detected in a specified repository (REPOSITORY-NAME), for example: repo:octo-repository. |
resolution | Display alerts closed as "false positive" (false-positive), "hidden by config" (hidden-by-config), "pattern deleted" (pattern-deleted), "pattern edited" (pattern-edited), "revoked" (revoked), "used in tests" (used-in-tests), or "won't fix" (wont-fix). |
secret-type | Display alerts for a specific secret type (SECRET-NAME), for example, secret-type:github_personal_access_token. For a list of supported secret types, see Supported secret scanning patterns. |
sort | Display alerts from newest to oldest (created-desc), oldest to newest (created-asc), most recently updated (updated-desc), or least recently updated (updated-asc). |
team | Display alerts owned by members of the specified team, for example: team:octocat-dependabot-team. |
topic | Display alerts with the matching repository topic, for example: topic:asdf. |
validity | Display alerts for secrets with a specific validity (active, inactive, or unknown). For more information about validity statuses, see Evaluating alerts from secret scanning. |