关于来自code scanning的警报
可配置 code scanning 为使用默认 CodeQL 分析、第三方分析或多种类型的分析检查存储库中的代码。 分析完成后,生成的警报将并排显示在仓库的安全视图中。 来自第三方工具或自定义查询的结果可能不包括所有你在默认的GitHubCodeQL分析检测到的警报中看到的属性。 有关详细信息,请参阅 配置代码扫描的默认设置 和 配置代码扫描的高级设置。
默认情况下,code scanning 会在默认分支及拉取请求中定期分析代码。 有关管理拉取请求上警报的信息,请参阅 鉴定拉取请求中的代码扫描警报。
你可以使用 GitHub Copilot自动修复 自动为code scanning警报(包括 CodeQL 警报)生成修复方案。 有关详细信息,请参阅“解决代码扫描警报”。
对于来自 code scanning 分析的CodeQL警报,你可以使用安全概述来查看 CodeQL 在组织内各存储库的拉取请求中的表现,并确定可能需要采取操作的存储库。 有关详细信息,请参阅“CodeQL 拉取请求警报指标”。
可以使用 code scanning 工具审核为响应GitHub警报而执行的操作。 有关详细信息,请参阅“审核安全警报”。
关于警报详细信息
每个警报都会高亮显示代码的问题以及识别该问题的工具名称。 你可以看到触发警报的代码行以及警报的属性,例如警报严重性、安全严重性和问题的性质。 警报还会告知该问题第一次被引入的时间。 通过 CodeQL 分析识别的警报,您还会看到有关如何解决问题的信息。
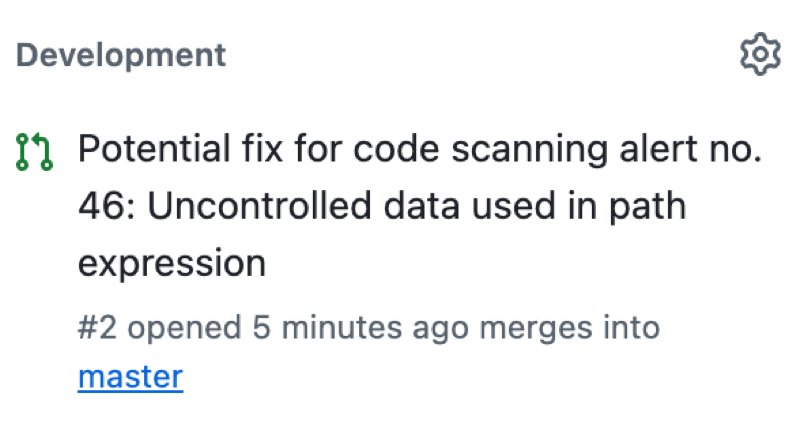
警报页面上的状态和详细信息仅反映存储库默认分支上的警报状态,即使警报存在于其他分支中也是如此。 可以在警报页右侧的“受影响的分支”部分查看非默认分支上的警报状态。 如果默认分支中不存在警报,则警报的状态将显示为“在拉取请求中”或“在分支中”,并将变为灰色。 “开发”部分显示将修复警报的链接分支和拉取请求。****
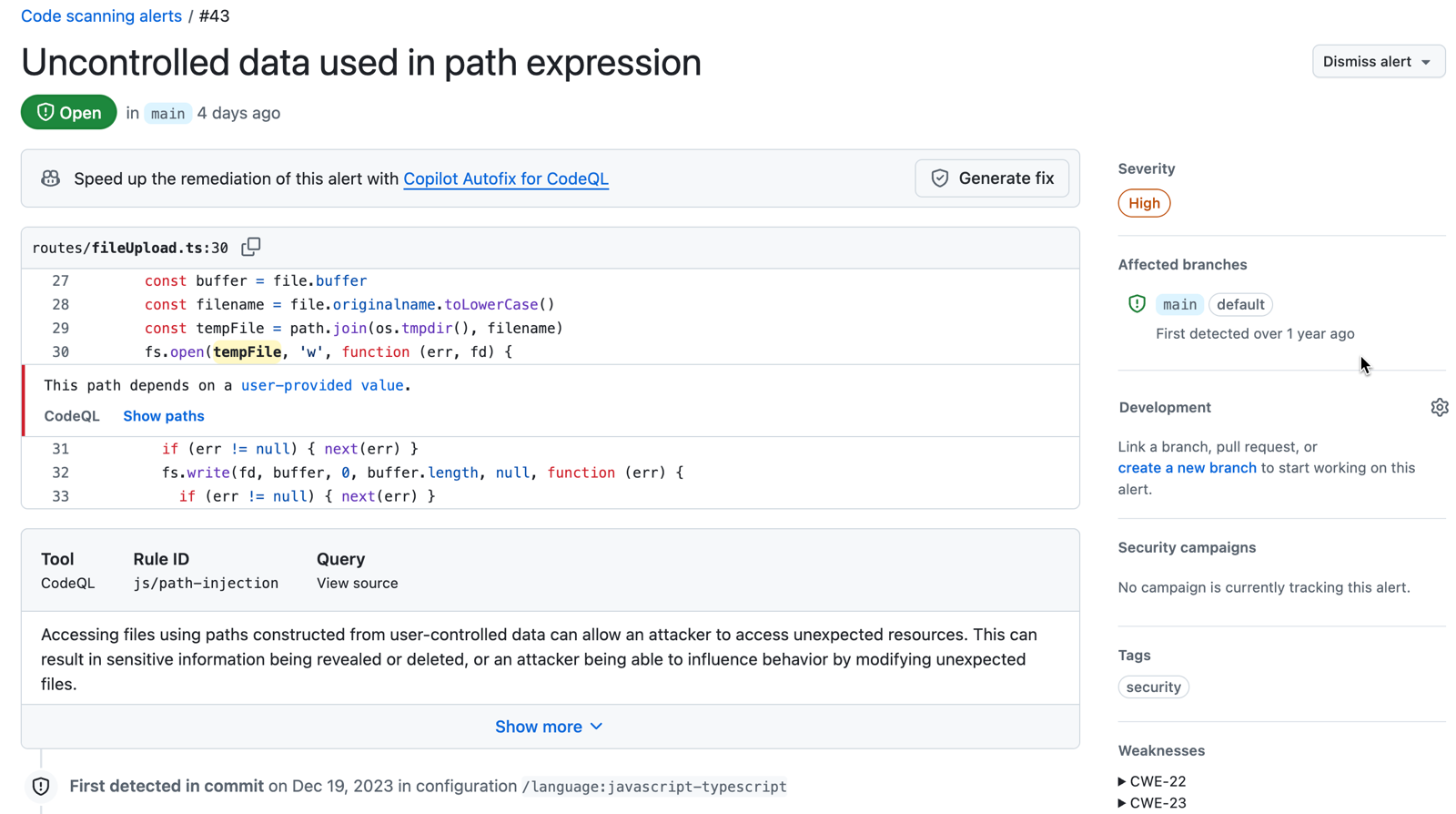
还可以查看受影响的分支,以及警报的修复内容和关联的拉取请求。 这有助于你和你的团队随时了解解决警报的进度。
如果使用 code scanning 配置CodeQL,还可以在代码中发现数据流问题。 数据流分析将查找代码中的潜在安全问题,例如:不安全地使用数据、将危险参数传递给函数以及泄漏敏感信息。
当 code scanning 报告数据流警报时,GitHub 会显示数据在代码中的流动方式。 Code scanning 允许识别泄露敏感信息的代码区域,这可能是恶意用户攻击的入口点。
在某些情况下,可以通过多个代码路径访问相同的漏洞,例如,当多个不同的函数将用户输入传递到相同的不安全操作时。 Code scanning 将这些相关路径分组到单个警报下,而不是为每个路径创建单独的警报,以便可以在一个位置查看漏洞的完整范围。
若要在没有离开 GitHub 的情况下跟踪团队工作流中的修正工作,可以将警报链接到问题。 请参阅“将代码扫描警报链接到 GitHub 议题”。
关于来自多个配置的警报
可以使用不同的工具和针对代码的不同语言或区域,在存储库上运行多个代码分析配置。 每个配置都会生成一组唯一的 code scanning 警报。 例如,使用带有 CodeQL 的默认 GitHub Actions 分析生成的警报,其配置不同于外部生成并通过code scanning API 上传的警报。
如果使用多个配置来分析文件,同一查询检测到的任何问题都将报告为多个配置生成的警报。 如果警报存在于多个配置中,则配置数会显示在警报页面右侧“受影响的分支”部分的分支名称旁边。 若要查看警报的配置,请在“受影响的分支”部分中单击分支。 此时将显示“配置分析”模式,其中包含生成该分支警报的每个配置的名称。 在每个配置下,可以看到该配置的警报上次更新的时间。
警报可能会显示不同配置的不同状态。 若要更新警报状态,请重新运行每个过时的配置。 或者,可以从分支中删除过时的配置,以删除过时的警报。 有关删除过时配置和警报的详细信息,请参阅 解决代码扫描警报。
关于应用程序代码中未找到的警报的标签
GitHub 将类别标签分配给应用程序代码中找不到的警报。 标签与警报的位置相关。
- Generated:生成过程生成的代码
- Test:测试代码
- Library:库或第三方代码
- Documentation:文档
Code scanning 按文件路径对文件进行分类。 无法手动对源文件进行分类。
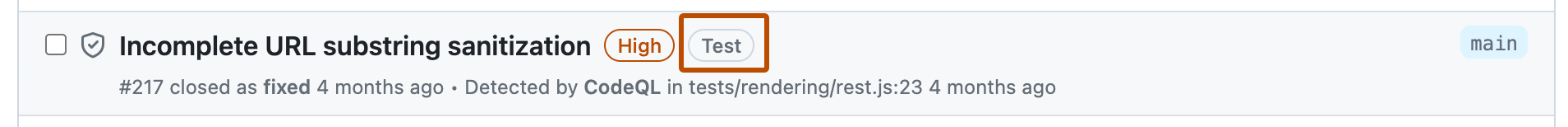
在此示例中,警报在code scanning 警报列表中被标记为“测试”代码。
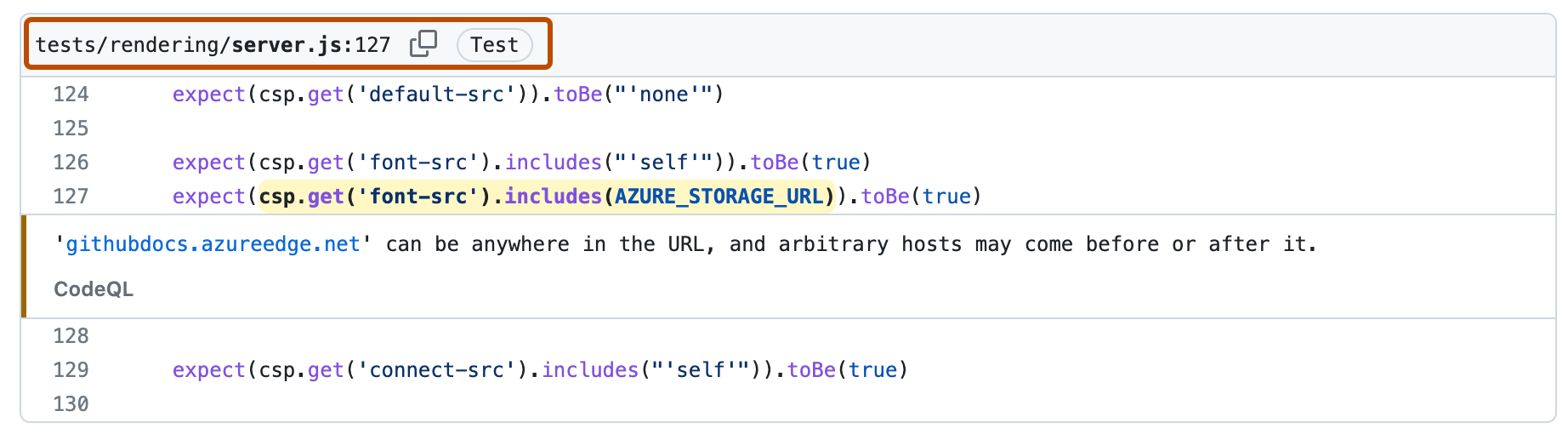
单击以查看警报的详细信息时,可以看到文件路径被标记为“测试”代码。
注意
针对code scanning的实验性警报可在 JavaScript 的公开预览版本中使用,该版本在 CodeQL 操作中使用了实验性技术。 此功能已退休。 有关详细信息,请参阅 CodeQLcode scanning 弃用由 ML 驱动的警报。
关于警报严重性和安全严重性级别
警报的 code scanning 严重性级别指示问题对代码库风险的增加程度。
- 严重性。 所有 code scanning 警报的级别为
Error、Warning或者Note。 - 安全严重性。 使用CodeQL的每个安全警报都具有安全严重级别
Critical、High``Medium或Low。
当警报具有安全严重性级别时, code scanning 显示并使用此级别优先于此 severity级别。 安全严重性级别遵循行业标准通用漏洞评分系统(CVSS),该系统也用于公告。GitHub Advisory Database 有关详细信息,请参阅 CVSS:定性严重性评定标准。
安全严重性级别的计算
将安全查询添加到 CodeQL 默认或扩展查询套件时, CodeQL 工程团队将计算安全严重性,如下所示。
- 搜索分配了与新安全查询关联的一个或多个 CWE 标记的所有 CVE。
- 计算这些 CVE 的 CVSS 分数的第 75 百分位。
- 将该分数定义为查询的安全严重性。
- 显示查询找到的警报时,使用 CVSS 定义将数值分数转换为
Critical、High、Medium或Low。
有关详细信息,请参阅文档网站上的CodeQLCWE 覆盖范围CodeQL。
关于拉取请求中的警报
Code scanning 警报可以在拉取请求上显示为检查结果和批注。 在以下任意一种情况下,code scanning 存储库中会发生这种情况:
- 配置为拉取请求检查(默认情况下,这仅限于针对默认分支的拉取请求)
- 配置为在每次推送代码时进行扫描(结果将被映射到所有打开的拉取请求)
只有当警报标识的代码行全部都存在于拉取请求差异中时,才会在拉取请求中看到警报。
根据分支保护规则,“Code scanning结果”检查可能是一项强制性检查,在通过该检查之前将阻止拉取请求被合并。